Azure Active Directory
The Azure Active Directory is the main directory for all of your online users, groups, contacts, and configuration. It is a good idea to have a daily/weekly look into the Azure Active Directory subscopes described below.
Directory synchronization
If you synchronize your identities from local Active Directory to Azure Active Directory, then you have a directory synchronization service active. At a small company and with only a few administrators there are not many errors that are coming up but have a daily or weekly look at the synchronization service in case of errors.
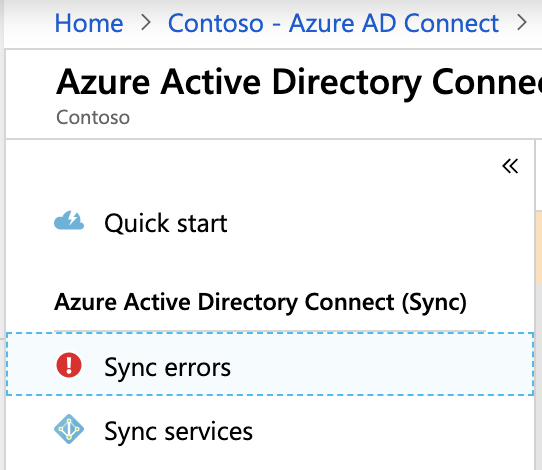
If your company is big and you synchronize more than one Active Directory Forest you can errors when synchronizing identities. The errors will be shown here “image above” and at the synchronization service at the Azure Active Directory Connect server. If you get an error try to fix the issue to solve the error. In most cases, the errors are attribute related, take care that your source identities are configured correctly.
These attributes must be unique in all connected Active Directories:
- UserPrincipalName
- ProxyAddresses/EmailAddresses
- Nickname/Alias
Microsoft articles:
- How to fix attribute value must be unique
- Identity synchronization and duplicate attribute resiliency
It is important that you train all your administrators that work on new identities in your on-premises Active Directory and if you have provisioning processes that create identities, take care that these processes need to be fit the new requirements of Azure Active Directory.
To initially check your on-premises identities try Idfix from Microsoft.
https://docs.microsoft.com/en-us/office365/enterprise/install-and-run-idfix
User settings
The first setting I set for a new Tenant is the user setting in Azure Active Directory.
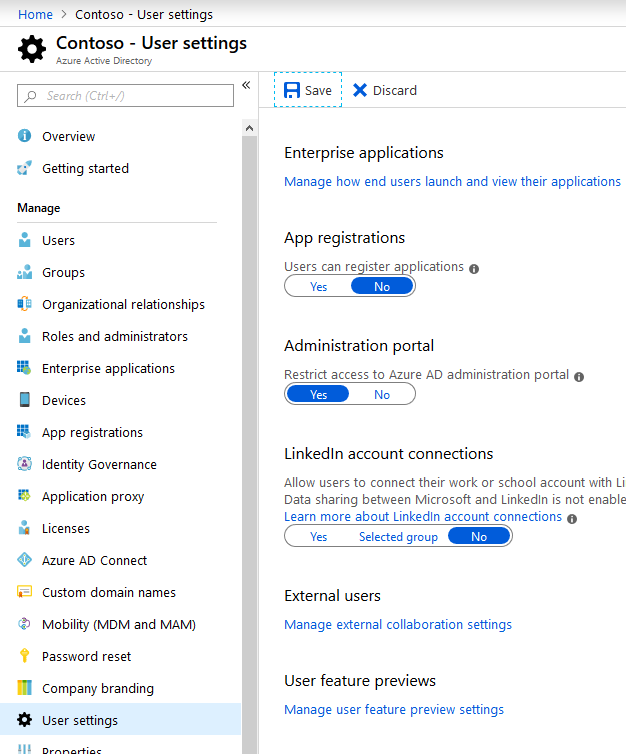
- App registration: Prevent users from registering custom deployed application.
- Administration portal: Restrict user from opening the administration portal. By default, non-administrative users can open the administrative portal and have read access.
- LinkedIn account connections: If your company does not have LinkedIn users, disable this option.
RSS Feed: https://docs.microsoft.com/api/search/rss?search=%22release+notes+for+azure+AD%22&locale=en-us
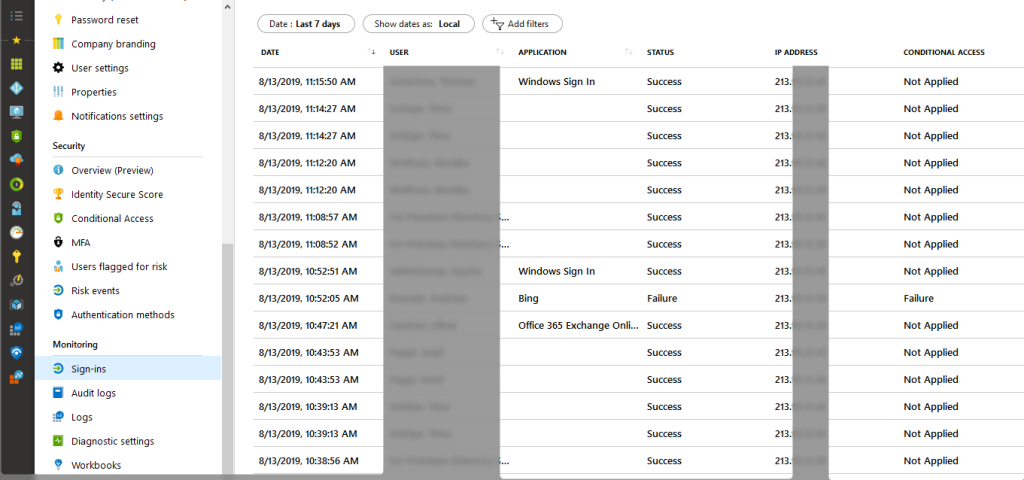
Azure AD Sign-ins
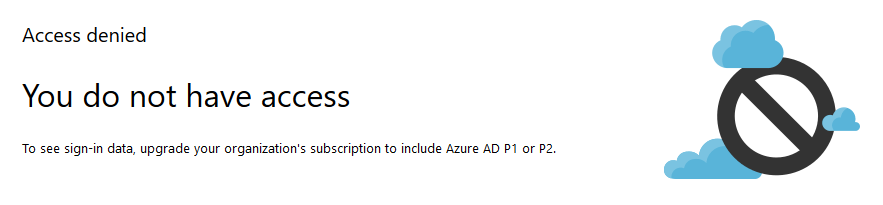
The login to Azure resources will be logged in Azure AD Sign-ins if you have the right license, if not you will see this message.
If you have an Azure AD Premium license, you will see the sign-ins here. You see every sign-in like successful or failed and you the through which application the sign-in was made. Take a daily or weekly look at the failed and successful sign-ins to see what happens in your Azure AD.
GEO DNS
Microsoft Azure and Office 365 supports GEO DNS for many services.
Even if your company is only located in one location, GEO DNS is a topic for you. I’ve seen Office 365 projects run slowly with mailbox migrations because the provider’s DNS servers didn’t support GEO DNS. For example, access to the Microsoft portals was slow because the DNS servers had returned hostnames from Office 365 or Azure that were hosted in completely different regions.
Please take care for each location that has an internet breakout, that the DNS servers that you use support GEO DNS. If you use Microsoft Active Directory on-Premises, you have to check your forwarder configuration on your Domain Controllers and I prefer to disable the root DNS server.
Secure Score
With Microsoft Secure Score in the Microsoft 365 security center, you can have increased visibility and control over your organization’s security posture. From a centralized dashboard, you can monitor and improve the security for your Microsoft 365 identities, data, apps, devices, and infrastructure.
Microsoft Secure Score gives you robust visualizations, integration with other Microsoft products, comparison of your score with other companies, filtering by category, and much more. With the tool, you can complete security improvement actions within your organization and track the history of your score. The score can also reflect when third-party solutions have addressed the recommended improvement actions.
Read more about the Secure Score at Microsoft
Have fun with Azure and Office 365
Arne